In today’s bulletin, Charlie gives his thoughts about Arnold Clark’s recent cyber incident and gives an insight into their response, and what we can learn from this.
For the last few weeks, I have been watching the news of the cyber-attack on Arnold Clark and thought that this week, I should write a case study of what we have learned to date about the attack, and review and comment on their response. The company is of personal interest to me as we bought two cars from them, their headquarters is just down the road from us, and they are a well-known and successful Scottish company.
I have no insider knowledge of their response and have used public sources for the details of what has happened. I have also used my knowledge of cyber security and knowledge gleaned from writing a number of cyber case studies – most notably on the SEPA hack – to write this article.
I thought as a framework for this bulletin I would use my “marks out of 100” framework to review their response.
About Arnold Clark
Arnold Clark, founded in 1954, is the UK’s largest independently owned, family-run car retailer. They pride themselves on offering customer service of the highest level, as well as the best choice and biggest discounts on all new cars, nearly new cars, used cars, new vans, and used vans. They provide servicing, MOTs, parts, motability, rental, and business vehicle leasing, have approximately 11,000 staff, and sell more than 300,000 cars a year. It has locations throughout the United Kingdom stretching from Elgin to Southampton. It is where people in Scotland tend to go to buy their cars, so most people in Scotland will have had some dealings with the company, as it has lots of franchises and it is a very visible company.
What Happened
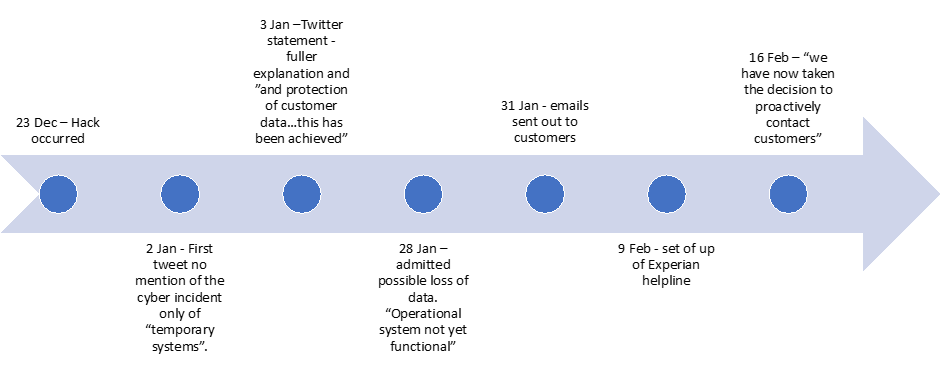
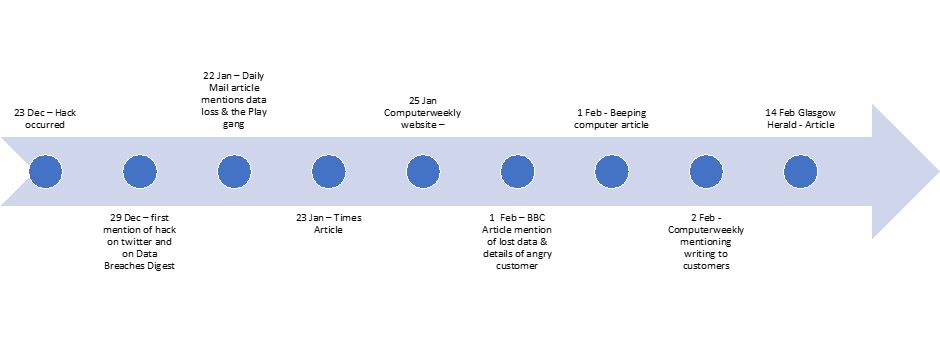
On the 23rd of December 2022 the company experienced a major cyber-attack, allegedly by the Play ransomware gang. The initial communication on the event was on Twitter on the 2nd of January 2023. The company said they were “using our temporary systems until we are able to restore full systems safely”, and didn’t admit that they had had a cyber-attack, making the problem sound like an IT outage. This first communication was swiftly followed by a tweet the next day saying that they took down their systems as a precaution, claiming that their actions prevented personal data from being stolen. They said “our priority has been to protect our customers’ data, our systems, and our third-party partners, While this has been achieved…”. In a statement on the 28th of January, they admitted they had lost company data and talked about the actions they were taking to support customers, which included setting up a call helpline with Experian, writing to affected customers, and providing 24 months of credit monitoring to those affected, free of charge. Emails were sent out to customers on the 31st of January and there have been two further communications on the 9th and 16th of February which said they have set up the helpline and said again that they will be contacting customers. A timeline of their communications is at Figure 1.
Review of their Response
So, was their response a slow-motion car crash? I have marked each element of their response with a score to give a total score out of 100. At the end of this bulletin, there are a couple of other organisation’s scores which you can compare this response against.
Business Impact
Impact on their business model and long-term ability to retain and grow customers
As Arnold Clark has several manufacturers’ brands within its portfolio, it is difficult to buy cars from other companies, so customers, unless they want to travel afar, have to use their services. As there is a waiting list for new cars, I suspect this incident will not have an impact in the medium term on the company. In the longer term, I think things are bleak for companies such as Arnold Clark with their existing business model. Brands such as Tesla do not sell through franchises and you can buy and configure your car online, so the franchise model could fade away. Electric cars need much less servicing than petrol and diesel cars so there will be less servicing work in the future, and the second-hand car market has been disrupted by the likes of Webuyanycar and Cinch. If there is anger amongst Arnold Clark’s customers over the way they have managed this cyber-incident, then they may buy from other providers, but if they want convenience, they will continue to buy at Arnold Clark.
Marks out of 15 – 10
2. The standing of the organisation before the cyber-incident and the loyalty of its customers
On Trustpilot, Arnold Clark has a score of 4.6 and their positive reviews far outweigh their negative ones, so they have a reasonable reputation. I think everyone in Scotland seems to have an Arnold Clark story, many of them negative. They have a reputation for being good at selling cars, but perhaps not so good at after-sales. As customers have nowhere else to go, they will continue in the short to medium-term buying from the company.
Marks out of 5 – 4
Response
3. Public and media sentiment on how well the incident has been managed
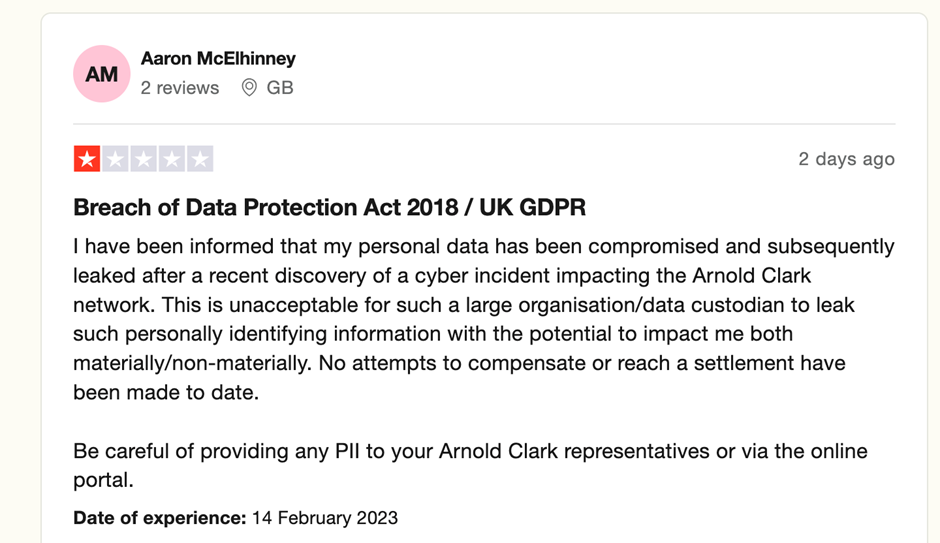
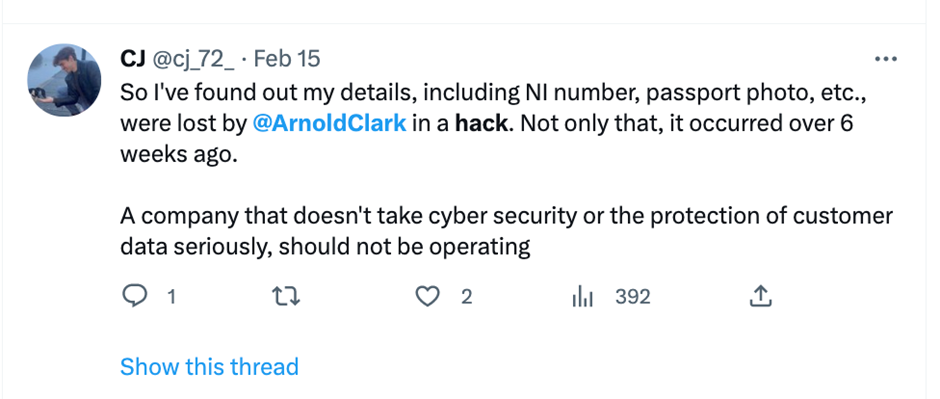
Although I think their response, especially the communications, has been poorly handled, there has been no sustained criticism of them in the press. The only negative press story about a disgruntled customer has been posted on the BBC website on the 1st of February. Almost all of the stories I have seen on new websites have been reporting the facts, rather than expressing an opinion on how well the hack has been handled. There has been a negative review on TrustPilot (Figure 2), and a couple on Twitter (Figures 3 & 4), but to date, there has not been any sustained criticism. There were some complaints on Facebook when their systems were down just after Christmas, but this was mainly about their inability to say that their systems were down.
For the media, this incident follows the same playbook as most other cyber incidents. As there is very little information released on the incident, the majority of the articles produced by newspapers and news websites, are rehashes of the information posted by the company on their website. The only difference in this incident is the breaking of the data available on the dark web by a newspaper, rather than coming from the company.
Marks out of 10 – 7
4. Time between discovering the hack and informing those affected
When I teach cyber incident management, I tell students as soon as they hear an organisation has had a cyber incident that has had any major impact on the organisation, or they admit to having a ransomware attack, you can likely deduce two things. Data is likely to have been locked and will have been exfiltrated. It may take some time for the organisation to confirm that data has been lost and what the data is, but you have to work on the presumption that data has gone outside of the company. Often, the ransomware gang will contact you and tell you in the ransom note that they have your data, so you can’t pretend that you don’t know data has left the organisation.
Initially stating that Arnold Clark believes that no data has gone is naïve, and shows a lack of cyber understanding. Many organisations get around this dilemma of suspecting that data has gone by saying “we believe no data has gone”, which leads them to later say that “we can now confirm after our investigations data has gone”. It was the Daily Mail which broke the story of the loss of data (click here for this article) and informed their readers that 15 GB of Arnold Clark’s data could be found on the dark web and the Play gang had another 476 GB in their possession, which they would release if a payment was not made.
Presuming that Arnold Clark was aware of the Daily Mail article, it took them another 7 days to put out their own information on the data leak, and seemed to send out the first communications by email on the 31st of January. The complainant in Figure 3 claimed he was made aware his data was lost on the 15th February and rightly said that he was only informed 6 weeks after the hack.
Organisations are in a difficult position if they suspect that data has gone but they don’t know whether they should inform those affected. They have within 72 hours under GDPR regulations to inform those whose data has been lost, but suspecting data has been lost is different from categorically knowing that data has been exfiltrated. From the beginning you must be open and honest with those whose data you hold, of the possibility of data loss. This should be done even before you know emphatically, as it shows that you have those whose data you hold’s interests at heart, and they will be angry when they think that the company has been sitting on the information in their own interest, and not informing them.
Marks out of 10 – 2
Communications
5. Appropriate media strategy and tone used to frame communications
Overall, I think Arnold Clark’s communications have been poor. The tone given in all statements and in the information given to customers has been very corporate, factual, and matter of fact. There is no empathy or contrition in the statements, only one apology. This is a B2C business whose website on the front page says, “pride ourselves on offering customer service of the highest level”. For a business which thrives on the customer relationship between the person selling the car and the customer, the media strategy has not been thought through – it is cold and is not customer-focused.
Marks out of 10 – 4
6. Appropriate and timely information on the incident is being provided to those who need it
Throughout the entire incident, the company’s communications have been reactive to events and it has taken them days to comment on events and information which is in public view. It took them from 23rd December to the 3rd January to admit they had had a cyber-attack, even when it was obvious to their customers, as they couldn’t collect their new cars. The first article (which can be found here) and tweet breaking the news that the company had had a cyber attack was on the 29th of December, five days before the company admitted to it occurring. The Daily Mail broke the story about data loss and the amounts which had been lost. If we look at the media timeline (Figure 5), against the company communications timeline, Figure 1, we can see that Arnold Clark’s communications have always been reactive, and other sites have broken the news before them.
There is a very important missing bit of information from Arnold Clark’s communications. There is no indication of whose data has been lost on its website postings. It was mentioned in a Herald article that the data lost might refer to people who have taken out credit with the company after 2019 but there is no mention of this in any of their communication. Should I worry if I was a past employee of the company, if my car had been serviced, or if I was a supplier? By not giving this information, I have no idea if I am affected until I get an email. If I have changed my email address, then it is likely I will not be contacted, and so, I will not know if I am at risk. Arnold Clark should be clear on who is and who is not at risk. If they don’t know, then tell us, and we can then decide if we want to take precautions.
Marks out of 10 – 4
7. Use of the website to provide information to those affected
As stated above there isn’t information on the website about who has been affected. On the website, there have only been 3 posts of information in 6 weeks. If Arnold Clark was a truly customer-focused company, they would post regular information relevant to the needs of their customers.
The website provides contradictory information. An email went out to people affected on the 31st of January and I have seen a copy of the information given, posted on Twitter, but on the 16th of February, they said “we have now taken the decision to proactively contact customers who may have been affected to make them aware of the cyber incident”. This looks like they have only now decided to tell customers. Re-reading the website articles, they seem to have been put together with not much thought and seem a bit of a random collection of comments, and that whoever is writing them is not a communications professional, or has had no training in crisis communications.
Arnold Clark, if you are using a PR company, sack them and get a new one. If not, find a good PR company that should be able to provide a much better communications strategy and copy. The website is a good place to put lots of information on the incident. People are only going to go on the website if they are interested in information on the cyber incident, and as newspapers use the text, it is a good opportunity to convey the good things you are doing, and perhaps put on a human story or two of how your staff have gone ‘above and beyond’ to respond, and provide service to your customers.
The company has followed good practice by putting a link to the cyber incident information on the front of its website. It is not too prominent to put customers off browsing the website, but it does signpost them to updated information.
Marks out of 10 – 4
8. Providing support to victims and where they can go for help. Timeliness of this help provided.
Arnold Clark has followed good practice and provided Experian’s Credit mentoring service for 24 months for those affected and has sent up a helpline manned by Experian. I haven’t tried it yet, but I wonder what service Experian is going to provide. Can they tell me if I have been affected or can they just give out general advice?
Marks out of 10 – 8
9. Visibility of senior managers / CEO
In all communications, there has absolutely been no visibility of the CEO in the response. No sign of media statements, interviews, apologies, or piece to camera hosted on the website. The Chief Executive and Group Managing Director, Eddie Hawthorne, did have time to do an interview on Twitter on the 25th of January about the upcoming Arnold Clark Cup, but did not do anything on the cyber incident. I am a great believer in leadership from the top, and in major incidents, the CEO should be seen to lead and be visible in the response.
Marks out of 10 – 1
10. Using social media channels to signpost fuller information on the hack
Social media was used at the beginning of the incident to provide information as the website was down, but since then, the various Arnold Clark social media channels have been used for sales advertising. It is important for the company to continue to sell during a cyber incident as customers want to buy and they must keep revenue coming in, but if you want to get information out to potential victims and give them advice, then social media can be a good way of signposting people to see a fuller explanation on the website.
Marks out of 10 – 4
Conclusion
As an academic exercise, I have not been impressed by Arnold Clark’s response. They have had no media strategy; their communications have not been thought through, and they always seem reactive by putting out communications. They failed to acknowledge that the issue was a cyber incident for 10 days which very much had echoes of the Travelex response. They said that they had taken steps to prevent data leakage and they had to admit that these were ineffective, and it was the Daily Mail which broke the story of their data loss. They lost 467 GB of data but took weeks to actually confirm and tell customers that they actually lost it. They don’t seem to have demonstrated much incident preparation in terms of training and exercising.
Whether this will have a long term effect on the company is less certain. Companies get hacked all the time and we get used to the idea that our data may have been lost and we take our own appropriate precautions in response to this. There is not a huge choice when it comes to buying a new car and if Arnold Clark is convenient and will sell them the car they want, customers will overlook the hack. There will be a few people who will complain and, of course, the lawyers are gathering people for a class action. I have seen calls for people to register on three different sites, but in the end, I think this cyber incident will not have a major impact on the organisation.
Total marks out of 100 – 48