This week, Charlie discusses the ‘cyber incident’ affecting Royal Mail and gives an insight into his recent ‘Cyber Course for Non-Cyber Roles’.
Twice this week, I delivered a day-long NCSC certified course – ‘Cyber Course for Non-Cyber Roles’ – as an in-house course for an organisation wanting to make sure that those in support roles have general cyber knowledge, are aware of the preparation they can do in advance of a cyber incident, and how they would respond. We mentioned the Royal Mail ransomware attack on the course so I thought I would share some comments on the attack and their response.
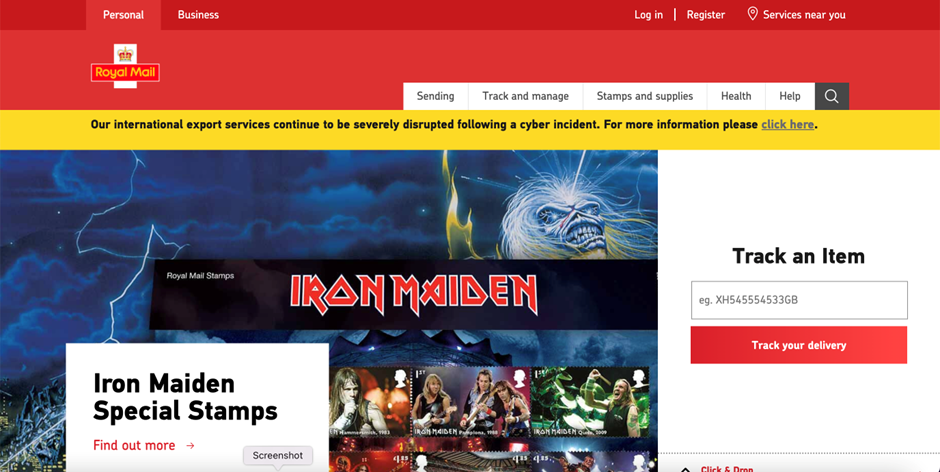
- We were talking on the course about whether organisations should admit to a cyber attack. My own opinion is that if you are a B2C organisation and hold lots of external personal data, you have to declare it so those whose data you hold are aware of it. I also think if you are a public body providing a service to the public, like the Royal Mail, you need to admit to the attack because you are not providing normal service. If an organisation is not in either of these two categories, then there seems a general trend (my thoughts, not scientifically proven), that organisations will try and limit as much as they can to admitting to a cyber incident. Funky Pigeon, the internet card and gift company, had a cyber incident. They are a B2C company, and had information on the cyber incident buried deep in their website which was only there if you wanted to find it. Coming back to Royal Mail, they have been open about the attack and have a prominent banner on the front page of their website. I haven’t been into one of their shops so I’m not sure whether there is a notice in their shops informing customers about the attack. The danger for organisations, if they sell through their website, is that every time a customer goes to buy, there is a large banner reminding them that the organisation has had a cyber attack. I am sure some of those who see the banner change their mind and go elsewhere to purchase their item.
- I think it is interesting that only their overseas parcels are affected by this incident. With previous ransomware attacks, such as on SEPA, and those affected by NotPetya – like Maersk or DLP Piper – it took out almost their entire IT infrastructure, including telephones. This seems to happen less often. As IT systems get better segregated, attacks can only get into, and attack one part of the network, without being about the attack and bring down the entire network.
- The following is the latest information on their website giving details of the actions they are taking.
Figure 1 Information on the Royal Mail website a click through from their front page banner.
A number of things strike me:
a) They are unable to use their main systems and have to rely on workarounds. After a ransomware attack, it takes a long time to get your existing systems up and going again so you have to rely on workarounds. With physical items like parcels, this is possible, but if your whole business is internet or computer-based, workarounds may be impossible. According to the BBC, Royal Mail ships 150 million parcels a year, so this volume is very difficult to handle manually.
b) One of the lost techniques in business continuity is thinking about the ‘backlog trap’. I don’t hear it mentioned very often. This is where your systems are disrupted, and the inputs keep coming – you never catch up and the backlog gets larger and larger. Royal Mail have asked customers not to submit any new overseas parcels.
c) The mention of customs declaration and being able to send an international letter which doesn’t require a declaration, seems that they have lost the link into international customers’ systems, which is then very difficult to conduct manually. Managing the recovery of interfaces with third parties is an important part of your cyber response.
d) They apologise, which is good!
4. Many of the comments on the attack mention that the LockBit ransomware was used to propagate this attack. A key part of incident response is understanding what ransomware has been used to attack you. This can provide very useful intelligence to your crisis team in understanding who may have attacked you, and the nature of the attack. So, build into your cyber response playbook for your crisis team to be informed about the software which has been used.
5. Most of the newspaper reports on the incident mirror the above information given out by the organisation. Use of your website to give details of the attack, and being about to give information about your successes, can be a good way to provide positive information to the media, which they will likely use in their coverage of the event.
6. The report on the SEPA cyber attack stated that they had a “high reliance on the goodwill of staff”. Royal Mail staff are in dispute with the company, with future strike days planned. Conducting a cyber response without the goodwill of staff must be difficult.
7. I found this on Edinburgh live – “A Royal Mail distribution centre in Northern Ireland revealed its printers began “spurting” out copies of a ransom note on Tuesday, saying “your data is stolen and encrypted.” I haven’t heard this before – attackers communicating with the company they have hacked!
8. To date, there is no mention of the exfiltration of data which usually happens with ransomware attacks.
9. Some of the newspaper articles criticise Royal Mail for not being over-open on the effects and nature of the attack. They have also mentioned that they are using the words cyber incident rather than ransomware attack. The BBC said “The firm is still referring to the cyber-attack as a “cyber incident” and is refusing to say publicly that it is ransomware, days after reporters confirmed it. These distinctions matter because ransomware attacks often involve the encryption, destruction, or theft of company, and sometimes customer data.” Often organisations in responding to a cyber attack use the excuse of the criminal element of the attack to provide very little information!
Although Royal Mail is now a private company because of its importance, they might provide a report on the incident once the event is over so we can all learn from this incident.